File this in the ever-expanding “Do As I Say, Not As I Do” section of your registrar irony file drawer. Alcumus, the mother company for registrar ISOQAR (UK) whose tagline is “Your Trusted Partner,” has admitted that it was inadvertently involved in a phishing scam. According to a (presumably legitimate) email blast that went out this morning from Alcumus’ Chief Technology Officer Mike Talbot, “an email purporting to be from an Alcumus employee (specifically Steve Stubley, Philip Goodland or Richard Edwards) requesting you review an online document or contract … was a phishing email.” Talbot went on to apologize for the threat, and indicated a list of really, really basic and really, really overdue things Alcumus did after the fact:
Reviewed (and continue to monitor) all account activity to identify other potentially compromised accounts and contained the risk appropriately
Issued a full internal communication regarding phishing attacks and password policies
In addition, we will shortly be introducing Office 365 Advanced Threat Protection system, which enhances our existing email spam filtering
You may remember Steve Stubley as the ISOQAR rep who previously refused to process an official complaint regarding its “Diamond” consultant referral scheme, where ISOQAR promised free booze and other gifts to consultants who convinced their clients to switch to ISOQAR registration. Stubley cited “confidentiality” as the reason he wouldn’t process the complaint, even as I cited “giggling to myself” as the result of his ridiculous excuse.
 Now Stubley — the same General Manager whose signature appears on ISOQAR’s ISO 27001 Information Security Management certification scheme (see image at right) — finds his email account “compromised” and his name slathered on dangerous phishing emails, while his bosses scramble to implement basic controls they should probably have put in place years ago.
Now Stubley — the same General Manager whose signature appears on ISOQAR’s ISO 27001 Information Security Management certification scheme (see image at right) — finds his email account “compromised” and his name slathered on dangerous phishing emails, while his bosses scramble to implement basic controls they should probably have put in place years ago.
The other two Alcumus geniuses cited are Lead Auditor Philip Goodland and Director of Business Development Richard Edwards, the latter of which claims to be an expert in — wait for it — risk management. Because of course he does.
This doesn’t necessarily mean Stubley, Goodland and Edwards did something dumb on their end which precipitated malware-ridden emails to go out with their names on them; often you can get an email with someone else’s name “spoofed” but with a totally different email address from some domain unrelated whatsoever to them. I get spoofed emails from myself all the time, from domains in Turkey and Russia, generated by “bots” who just scrape the internet for email addresses to attach to emails they send remotely. But Talbot’s letter appears to throw his own people under the bus, by suggesting solutions that target internal weaknesses.
Let’s unpack their three-step solution. First, to be taken at all seriously as a world arbiter of Infomation Security Management Systems, perhaps Alcumus should have been “monitoring account activity” of its IT systems and users long before the phishing attack put its customers and other in jeopardy.
The second bullet in Talbot’s list shows they sent an internal email around reminding Alcumus employees not to be stupid, which was apparently too late, since they’ve already hired stupid people. The idea that just re-communicating an existing policy is sufficient is laughable; it was that policy and the surrounding communication of it that likely caused this problem in the first place. Perhaps they need a new policy, and one that sticks? Like, “Hey, Stubley, do this again and you’ll find yourself working for Lloyds” or something.
Finally, the last bullet shows Alcumus planning to implement a Microsoft product that has been around since 2015 (!!), and one which IT security experts have panned for weak security controls. This means that first of all, Alcumus’ solution is not foolproof, but worse, they haven’t even implemented it yet.
So in effect, they’ve done nothing. But they keep selling ISO 27001 audit services with a yes-we-have-our-fingers-crossed-behind-our-backs straight face.
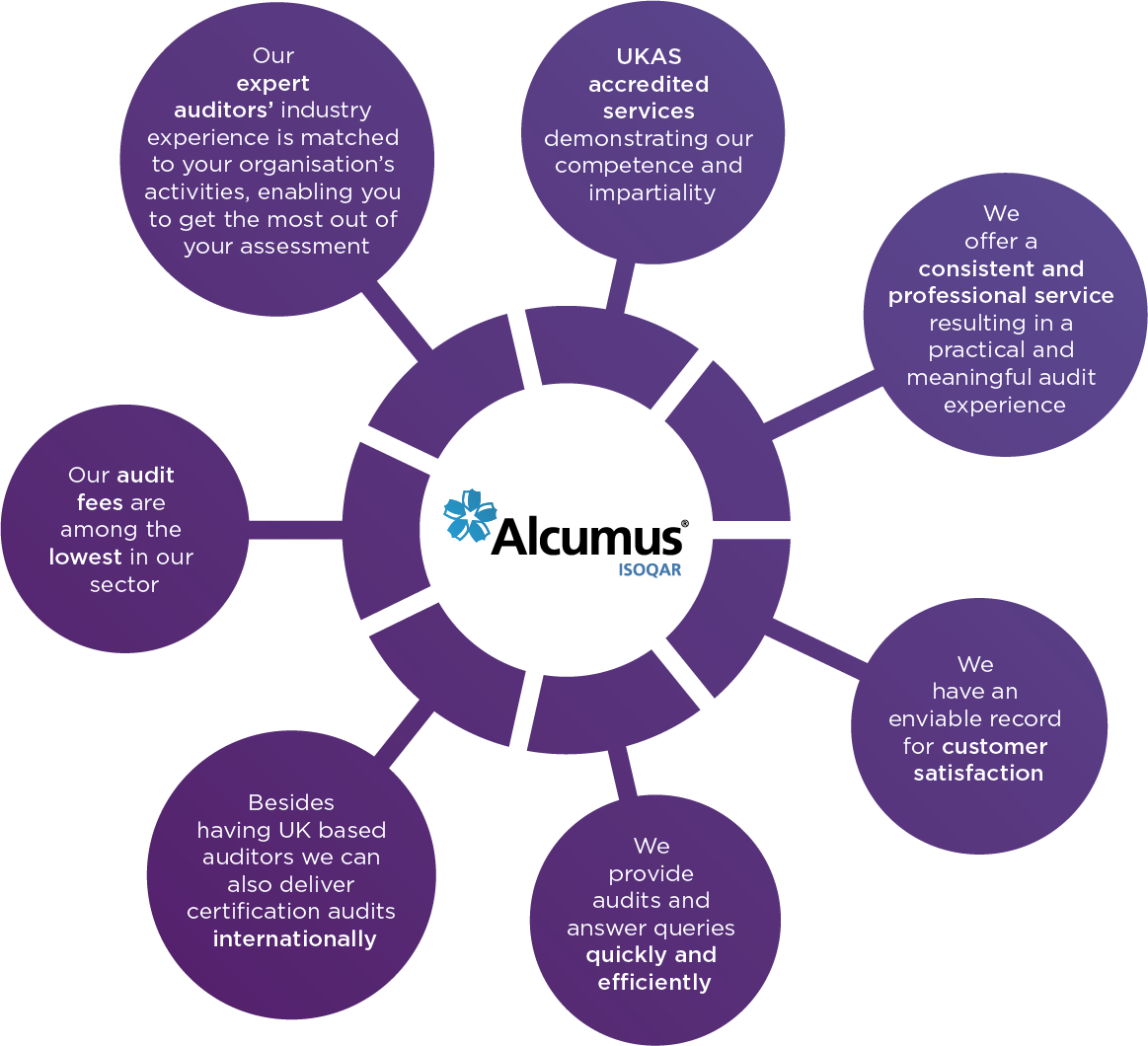
To be fair, Alcumus ISOQAR’s marketing of its ISO 27001 certification service doesn’t actually make any bold claims about its expertise in the information security area, a stunning difference between itself and its competitors which is notable by its absence. Instead, Alcumus ISOQAR’s major selling points for 27001 appear to be how cheap it is, how they can somehow “deliver certifications internationally” by despite having predominantly UK-based auditors (OK, that’s suspicious), and how they answer questions quickly. Of course, their answer might be “we can’t answer you because of confidentiality,” but at least you’ll get that answer in a speedy manner, along with some additional emails that ask you to click on a virus-laden .DOCX file.
It’s yet another slap in the face to the ISO certification scheme, showing that the so-called certifiers of other people’s management systems barely have functioning systems of their own, which (at this point) probably surprises nearly no one.
Can we rely on Alcumus ISOQAR’s accreditation body, UKAS, to take up this issue? I doubt it, since UKAS is probably too busy trying to update their own IT systems to Windows Vista while pleading with their own auditors to stop using AOL email addresses and submit reports via telegraph.
To read Talbot’s full email on the matter, click here. If you’re asked to send your bank account login details to claim your $25B inheritance from a prince in a country you never heard of, go right ahead, since Alcumus ISOQAR can totally be trusted with these things. Or, if you’re like me, you might be disappointed in knowing that the company you hired to certify your information security management system caused, instead, your information security to be put at risk.
NOTE: Alcumus ISOQAR is unrelated to the US-based registrar ISOQAR, Inc. from Bonita Springs FL; the two are wholly separate companies that happen to share a similar name.
Christopher Paris is the founder and VP Operations of Oxebridge. He has over 35 years’ experience implementing ISO 9001 and AS9100 systems, and helps establish certification and accreditation bodies with the ISO 17000 series. He is a vocal advocate for the development and use of standards from the point of view of actual users. He is the writer and artist of THE AUDITOR comic strip, and is currently writing the DR. CUBA pulp novel series. Visit www.drcuba.world