The CyberAB has hired Mathew Newfield as its new Executive VP and COO, a new salaried position created within the CMMC accreditation body. Newfield was Chief Information Security Officer (CISO) at Unisys; that company was charged “making materially misleading disclosures regarding cybersecurity risks and intrusions” at the time of Newfield’s employment there.
Per his LinkedIn profile, Newfield held the role of CISO at Unisys from 2018 to 2021, and then was promoted to SVP & Chief Security Infrastructure Officer, a position he held until 2023.
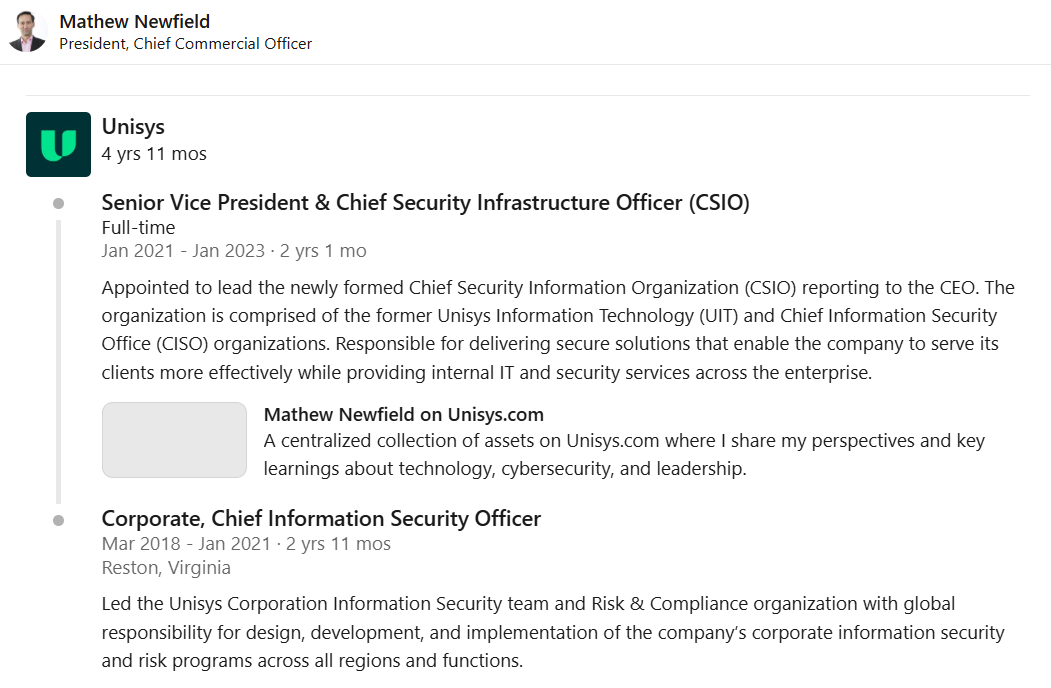
In official filings, the SEC charged Unisys with “materially misleading statements … regarding cybersecurity risks and events, as well as Unisys’s violations of disclosure controls and procedures requirements.” The company eventually paid $4 million in civil penalties.
The full charging letter may be read here.
The scandal arose after the Solar Winds cyberattack, thought to have originated from Russia. Per the SEC charge letter:
In December 2020, Unisys identified one computer in its network that had a version of SolarWinds Orion software, which a likely nation-state threat actor2 infected with malicious code that could have allowed for unauthorized activity on affected computers and their networks (“SolarWinds Compromise”). Unisys also received notifications about and discovered compromises of its environment likely by the same threat actor. The compromises of Unisys’s systems took place over a combined span of at least sixteen months starting in January 2020 and were persistent and impacted several parts of its corporate network and non-customer facing cloud environment. Specifically, the activity involved the compromise of at least seven network credentials3 and 34 cloud-based accounts, including those with administrative privileges, repeated connections into Unisys’s network with at least 33 gigabytes (“GB”) of data transferred, and access to cloud-based shared files and mailboxes, including those of senior IT personnel. Unisys was aware that its investigations of the compromise involved significant gaps in its ability to identify the full scope of the unauthorized activity due to the lack of availability of the forensic evidence.
Despite this, Unisys downplayed the impact of the Solar Winds hack, leading the SEC to charge the company with making materially false statements.
On February 26, 2021 and February 22, 2022, Unisys filed its annual reports for the years ending 2020 and 2021, respectively, on Form 10-K with the Commission. In both reports, Unisys negligently framed risks from cybersecurity events as hypothetical despite the company’s awareness of the SolarWinds Compromise-related activity, thereby rendering these disclosures materially misleading.
In 2022, Unisys faced another hack, stemming from “presence and execution of powerful password-stealing malware, Mimikatz, on seven computers in its non-customer facing software development network.”
The SEC reported that “Unisys’s cybersecurity personnel failed to report the 2020 and 2021 activity to disclosure decision-makers until a year after discovering it, and the 2022 extortion incident until the hackers’ public statement.”
All told, the scandal unfolded between 2020 and 2022, all covered by Newfield’s role in overseeing Unisys’ cybersecurity efforts as CISO. The annual reports cited by SEC (here and here) include Newfield’s name in the list of corporate officers.
Ironically, the Cyber AB and CMMC actors have threatened companies within the Defense Industrial Base that if they do not comply with CMMC, they will face False Claims Act charges.
CMMC Plagued with Scandal
The CyberAB and CMMC program have been hotbeds of scandals and ethics violations, as both the AB and the DOD CMMC Program Office ignore such problems in order to shove the certification scheme into being. The scheme was originally created by former DOD CIO Katie Arrington, who had her security clearances stripped from her after allegedly blurting out classified information during a meeting with non-cleared vendors. She resigned and then later sued the government for a “name-clearing hearing,” which she never won. She was temporarily brought back under the second Trump administration, but given limited duties and has since resigned again.
The CyberAB’s board has been repeatedly criticized for engaging in scandals and scams. The original AB head, Ty Schieber, was forced to resign alongside Board member Mark Berman for rolling out a pay-to-play “Diamond Member” program that would have given special privileges to those donating $500,000 or more.
The CyberAB has repeatedly refused to uphold its Code of Ethics, allowing known scammers to obtain official credentials. Complaints filed with the AB are then ignored. Despite claims to the contrary, Cyber AB Board members continue to profit from selling CMMC-related services, and those who have done so in the past have faced no repercussions.
The CMMC scheme has been characterized by Oxebridge as a made-up “rentseeking” scam, cooked up by Arrington and her consultant cronies to drive business their way. Oxebridge has argued that the DoD’s overnight creation of the AB itself was illegal, as the US cannot mandate the formation of a private company without the passage of a law.
The hiring of Newfield is likely to worsen the view of both the CMMC scheme and the CyberAB itself.